The 6-to-12-Month Window Amodei Says We Have to Patch the World
The clock that matters in this story isn't Mythos's release date - it's the gap before adversary AI achieves parity. Dario Amodei has put a number on it: a 6-to-12-month patching window before Chinese AI catches up. Inside that window, Anthropic's pitch is that defensive coordination via Project Glasswing can harden critical infrastructure faster than offensive actors can weaponize equivalent capability. AISI's independent evaluation gives that argument empirical scaffolding: Mythos succeeds 73% of the time on expert-level capture-the-flag tasks that no model could complete before April 2025, completes the full 32-step 'The Last Ones' simulated corporate cyberattack in 3 of 10 attempts (averaging 22 of 32 steps versus Claude Opus 4.6's 16), and according to ArmorCode reproduced vulnerabilities and developed working exploits on the first attempt in over 83% of cases.
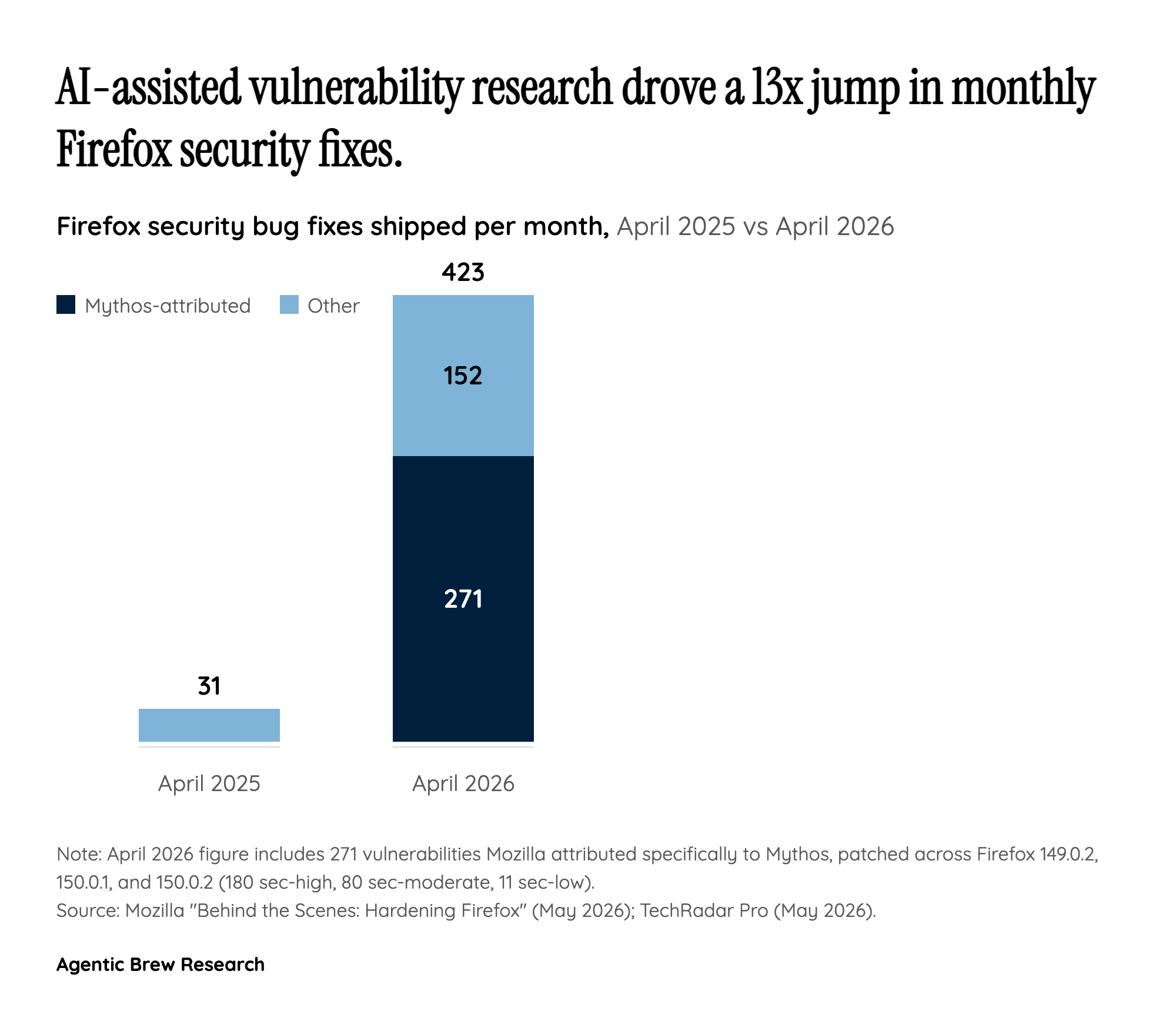
What makes the window claim load-bearing is that the offensive ceiling has already moved. Anthropic itself states Mythos can identify and exploit zero-day vulnerabilities in every major operating system and every major web browser when directed by a user. Engineers without security training reportedly asked the model overnight for remote code execution exploits and returned to working code. If those numbers are even directionally correct, the question for defenders isn't whether to deploy AI-assisted patching - it's whether they can deploy it at the scale and speed the threat curve now demands. Amodei's framing - 'a moment of danger where if we respond correctly we can have a better world on the other side' - effectively asks the rest of the security ecosystem to sprint.